PCI DSS Readiness 101: A Business Leader’s Guide to Mastering Compliance
- Mar 20
- 7 min read
In the modern digital economy, trust is the only currency that truly matters. For any organization handling credit card information, that trust is codified through the Payment Card Industry Data Security Standard (PCI DSS). However, for many business leaders, PCI DSS is often viewed as a daunting mountain of technical jargon and "checkbox" requirements.
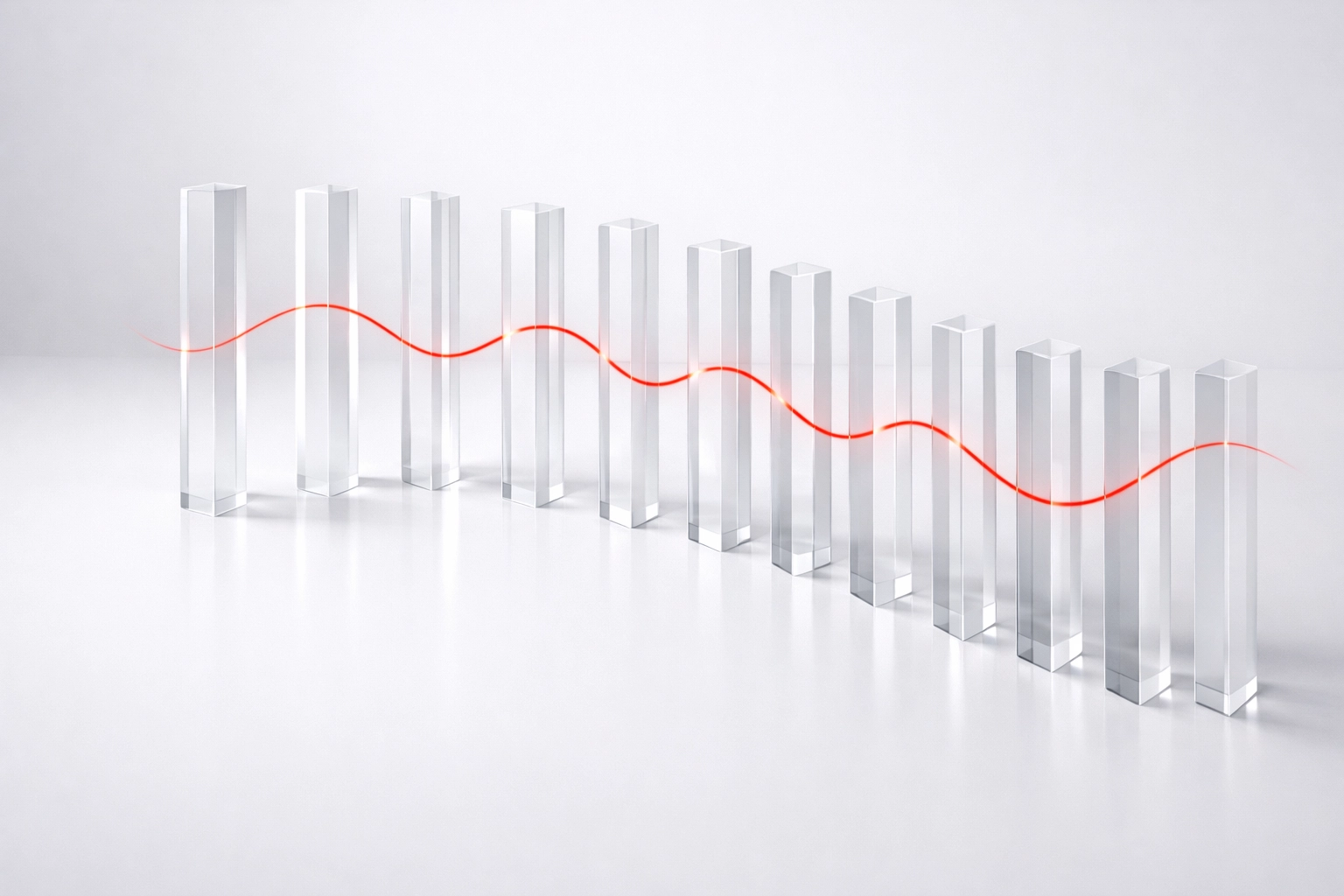
At Red Spider Security, we view it differently. We believe in the "Red Thread": the concept that compliance is not an isolated IT project, but a vital strand woven through the very fabric of your business resilience. When you master PCI DSS, you aren't just avoiding fines; you are hardening your infrastructure against the evolving threat landscape of 2026.
The Modern Challenge: Beyond the Checkbox
The reality of the current cyber landscape is that hackers do not care about your compliance certificates. They care about your vulnerabilities. If your approach to PCI DSS is merely a "tick-the-box" exercise performed once a year, you are leaving your organization exposed to catastrophic financial and reputational risk.
The Cost of Non-Compliance:
Hefty Monthly Fines: Ranging from $5,000 to $100,000 per month until compliance is reached.
Increased Transaction Fees: Banks may raise your processing costs as a "high-risk" merchant.
Brand Erosion: A single breach can destroy years of customer loyalty in seconds.
Legal Liability: Lawsuits from affected consumers and partners can lead to long-term insolvency.
To thrive, leaders must transition from a reactive posture to a proactive strategy. This begins with a comprehensive PCI DSS readiness assessment.

The 12 Pillars of PCI DSS: A Strategic Overview
While the technical requirements are exhaustive, they can be categorized into strategic pillars that every executive should understand. You do not need to know how to configure a firewall, but you must ensure your team has the resources to maintain these 12 core areas:
Network Security: Installing and maintaining firewalls to protect cardholder data.
System Configuration: Avoiding vendor-supplied defaults for passwords and security parameters.
Data Protection: Protecting stored cardholder data through encryption and truncation.
Transmission Security: Encrypting data as it travels across open, public networks.
Vulnerability Management: Using and regularly updating anti-virus software.
Secure Systems: Developing and maintaining secure systems and applications.
Access Control: Restricting access to cardholder data by business need-to-know.
Identification and Authentication: Assigning a unique ID to each person with computer access.
Physical Security: Restricting physical access to cardholder data and processing systems.
Monitoring and Tracking: Tracking and monitoring all access to network resources and data.
Regular Testing: Frequently testing security systems and processes.
Information Security Policy: Maintaining a policy that addresses information security for all personnel.
The 2025nd-2026 Shift: New Requirements for a New Era
As of 2025 and moving into 2026, the standard has evolved to be more outcome-based. Organizations are now required to demonstrate clearly defined roles and responsibilities for every single PCI DSS requirement—and to prove those assignments are understood, executed, and maintained. This isn’t paperwork for paperwork’s sake; it’s a critical signal of a mature program. When ownership is explicit, gaps surface faster, control drift is easier to spot, and audits stop feeling like a fire drill.
What has changed?
Formal Change Control: Any modification to your network must follow strict documentation.
Infrastructure Security: Files such as Terraform scripts and cloud configurations must be secured with the same rigor as the data itself.
Shared Responsibility Transparency: You must document exactly which requirements are managed by you and which are handled by third-party service providers.
This shift highlights why a generic approach no longer works. You need a partner who understands the nuances of these updates and can integrate them into your existing workflow without halting your operations.
Our Solution: The PCI DSS Readiness Assessment
How do you know if you are truly ready for a formal audit? You don't guess: you assess. A PCI DSS readiness assessment is a proactive "mock audit" designed to identify gaps before they become liabilities.
At Red Spider Security, our QSA-certified consultants (Qualified Security Assessors) bridge the gap between technical requirements and business objectives. We don't just hand you a list of problems; we provide a roadmap for resilience.
The Red Spider Process: Assess → Build → Maintain
We follow a three-step framework designed to minimize disruption while maximizing security.
1. Assess
Our team performs a deep dive into your current environment. We identify where cardholder data resides, inventory your IT assets, and analyze your payment processing workflows. We look for the "hidden" data: the spreadsheets or temporary files that often escape traditional scans but pose the highest risk.
2. Build
Once the gaps are identified, we help you repair them. This isn't just about software; it’s about process. We assist in securely removing unnecessary data storage, implementing robust access controls, and training your staff to recognize social engineering attempts.
3. Maintain
Compliance is a marathon, not a sprint. We help you establish automated audit trails and regular testing cycles. By the time your official audit arrives, it should be a non-event because your systems are already performing at the required standard every single day.

Why Expert Guidance is Non-Negotiable
You might be tempted to handle compliance internally to save on immediate costs. However, the complexity of modern payment environments: often spanning multiple cloud providers and third-party vendors: makes DIY compliance a dangerous gamble.
Here’s the hard truth: PCI programs don’t fail because teams are lazy. They fail because the details are easy to misread, evidence gets missed, and ownership gets fuzzy. We’ve seen the pitfalls so you don’t have to.
The Red Spider Advantage:
Current or Former QSA Leadership (Not “Just IT Guys”): Our consultants are current or former QSAs with decades of hands-on experience guiding organizations through readiness, audit expectations, and the real-world interpretation of PCI DSS. That perspective matters when an assessor asks for proof—not opinions.
Business Outcome Focus: We don't implement security for the sake of security. We implement it to protect your revenue, your reputation, and your future.
The Red Thread Methodology: We connect your PCI DSS efforts to your broader IT risk management strategy, ensuring that every dollar spent on compliance also strengthens your overall defense against cyber threats.
Identifying Your Scope: The Principle of Least Privilege
One of the most effective ways to simplify your PCI DSS journey is to reduce your "scope." If your systems don't touch cardholder data, they don't need to be compliant.
We work with you to implement the Principle of Least Privilege. By restricting data access only to those who absolutely need it for their job functions, we shrink the attack surface. This not only makes your organization more secure but also significantly lowers the cost and complexity of your annual assessments.

Signal Architecture Pass: Turning PCI Evidence Into Executive-Grade Signals
Most organizations aren’t short on “security activity.” They’re short on signals—repeatable, provable indicators that controls are operating as intended. A mature PCI program makes it easy to answer: What’s working? Who owns it? Can we prove it?
This is where we apply a Signal Architecture lens. We help you design PCI readiness so your evidence isn’t scattered across tools, inboxes, and tribal knowledge. Instead, it becomes a set of clear signals that stand up to scrutiny:
Ownership Signals (2025-2026 Maturity Marker): Named control owners for every requirement, with documented responsibilities and escalation paths.
Control Operation Signals: Tickets, logs, screenshots, configuration baselines, and attestations that consistently show the control is running—not “we think it is.”
Change Signals: Evidence that changes are reviewed, approved, tested, and traceable (especially for cloud/IaC and payment flow changes).
Vendor Signals: Proof that third parties are meeting shared responsibility obligations—and that you can demonstrate due diligence on demand.
The practical outcome: fewer surprises in audits, faster remediation, and leadership-level clarity you can rely on.
The Red Thread: PCI Readiness That Strengthens IT Risk Management and Strategic Planning
PCI DSS is a compliance standard, but the way you operationalize it should directly reinforce your broader security and business objectives. That’s the Red Thread.
IT Risk Management (ITRM): We translate PCI requirements into policies, standards, and procedures you can defend—then map gaps against frameworks like NIST, COBIT, ISO 27001, CIS Controls, and PCI-DSS so your risk posture improves beyond the cardholder environment.
Strategic Planning: We convert PCI remediation into a prioritized roadmap that aligns with budgets, timelines, and operational constraints—so compliance work becomes planned modernization, not reactive scramble.
The Reality: Are You Prepared for an Audit Today?
Ask yourself these three questions:
Do we have a current inventory of all locations where cardholder data is stored?
Can we prove that our third-party vendors are fulfilling their security obligations?
Have we updated our roles and responsibilities to meet the 2025-2026 standards?
If the answer to any of these is "I'm not sure," you are at risk.
Take the First Step Toward Resilience
PCI DSS compliance doesn't have to be a burden. When managed correctly, it becomes a strategic asset that streamlines your operations and provides peace of mind to your stakeholders.
Don't wait for a data breach or a failed audit to take action. Secure your business, protect your customers, and ensure your long-term resilience by partnering with experts who understand the "Red Thread" of security.
The Red Spider Advantage: Derek Little’s Three Big Questions (Answered)
If you’re evaluating partners, you’re likely asking the same three questions Derek Little calls out. You should.
1) Why Red Spider?
Because we don’t treat PCI as a once-a-year checkbox. We treat it as an operating model. We bring deep PCI expertise and connect it to the systems that keep your business running—risk management, governance, evidence, and execution. Most firms wash the car. We build the engine.
2) Why trust us?
Our readiness work is led by current or former QSAs with decades of experience. That means you’re not getting generic “IT advice.” You’re getting practitioner guidance shaped by how assessments actually work, how auditors interpret evidence, and where real programs commonly break down. We’ve seen the pitfalls so you don’t have to.
3) Where’s the proof?
We produce proof in the form that matters:
A documented scope and data flow you can defend
A mapped gap assessment with prioritized remediation
A practical roadmap tied to owners, timelines, and measurable outcomes
Audit-ready evidence signals (roles/responsibilities, control operation, change control, and vendor accountability) aligned to the 2025-2026 expectations
Ready to master your compliance? Contact our team of QSA-certified consultants today to schedule your PCI DSS readiness assessment.
Secure your perimeter. Protect your data. Build your future with Red Spider Security.
Comments